Exploiting CVE-2017-8759: SOAP WSDL Parser Code Injection
Introduction
CVE-2017-8759, the vulnerability recently discovered by FireEye as being exploited in the wild is a code injection vulnerability that occurs in the .NET framework when parsing a WSDL using the SOAP moniker. An overview of the vulnerability can be found in this post by FireEye and is recommended as pre-requisite reading.
This vulnerability was of particular interest to the ActiveBreach team as its weaponisation could be leveraged during our Adversary Simulation exercises. This post serves as a walk through on how to exploit this vulnerability without user interaction in the RTF file format.
Tutorial
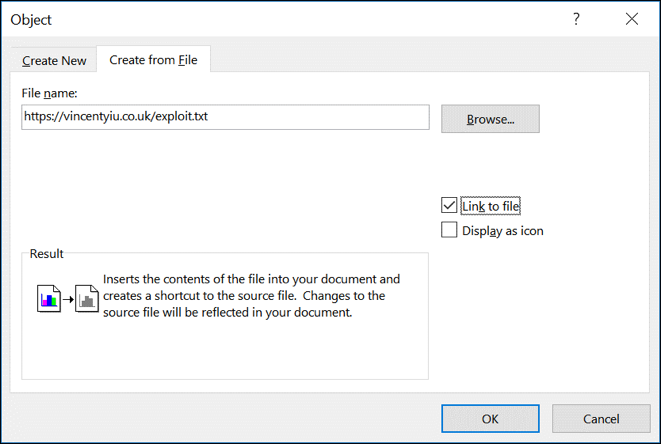
Firstly, create a new RTF document with a new OLE object using the steps similar to as described in our post on CVE-2017-0199.
Next, save the file as an RTF then reopen it using a hex editor and locate the “objdata” parameter to identify where the OLE blob is. When the parameter is located, add the “\objupdate” directive in a similar way to as described in our CVE-2017-0199 post.
Once this is complete, retrieve the “blob.bin” OLE blob from this GitHub repository, open it in a hex editor and update the URL of the WSDL file which contains the code injection. This OLE blob should now be used to replace the one in the existing RTF document.
At this point, on opening the RTF document the exploit should execute the HTA file pointed to in the WSDL, without user interaction.
An end to end video walk through of exploiting this vulnerability is shown below:
Happy hacking!
This blog post was written by @vysecurity of the ActiveBreach team.